Hello, this is IT Center Blog.
Company news from the first hand: everything that happened in IT Center yesterday, the day before yesterday and last Thursday. All publications are cleaned from white noise and synchronized with RSS feed.
Tags
All images © 2009–2023 www.svetlanalarina.com
Unauthorized use and/or duplication of text, photo and video material without express and written permission from IT Center Blog’s author and/or owner is strictly prohibited. Excerpts and links may be used, provided that full and clear credit is given to IT Center Blog with appropriate and specific direction to the original content.
The New Client's Office: Protection From Cyber Attacks

Another node was added to IT Center Cloud network: the Сustomer, with whom we are working for the seventh year, opened a new office in St. Petersburg.
This means that Check Point firewall works in the Сustomer's office now.

Check Point Software Technologies Ltd., the largest pure-play security vendor globally, provides industry-leading solutions, and protects customers from cyberattacks with an unmatched catch rate of malware and other types of attacks. Check Point offers a complete security architecture defending enterprises’ networks to mobile devices, in addition to the most comprehensive and intuitive security management.
Check Point’s products contain the world’s most advanced security technology. The Company currently holds 70 United States patents, more than 60 U.S. patents pending, and additional patents issued and patent applications pending worldwide.
Check Point Features
A box with a blue front panel encrypts network traffic between the data center and the Сustomer's office using site to site VPN protocol and between the offices and the customer's warehouses. In addition, Check Point automatically balances the network load between two independent network providers: in the event of a connection failure, the firewall will automatically take the network traffic to a working channel.
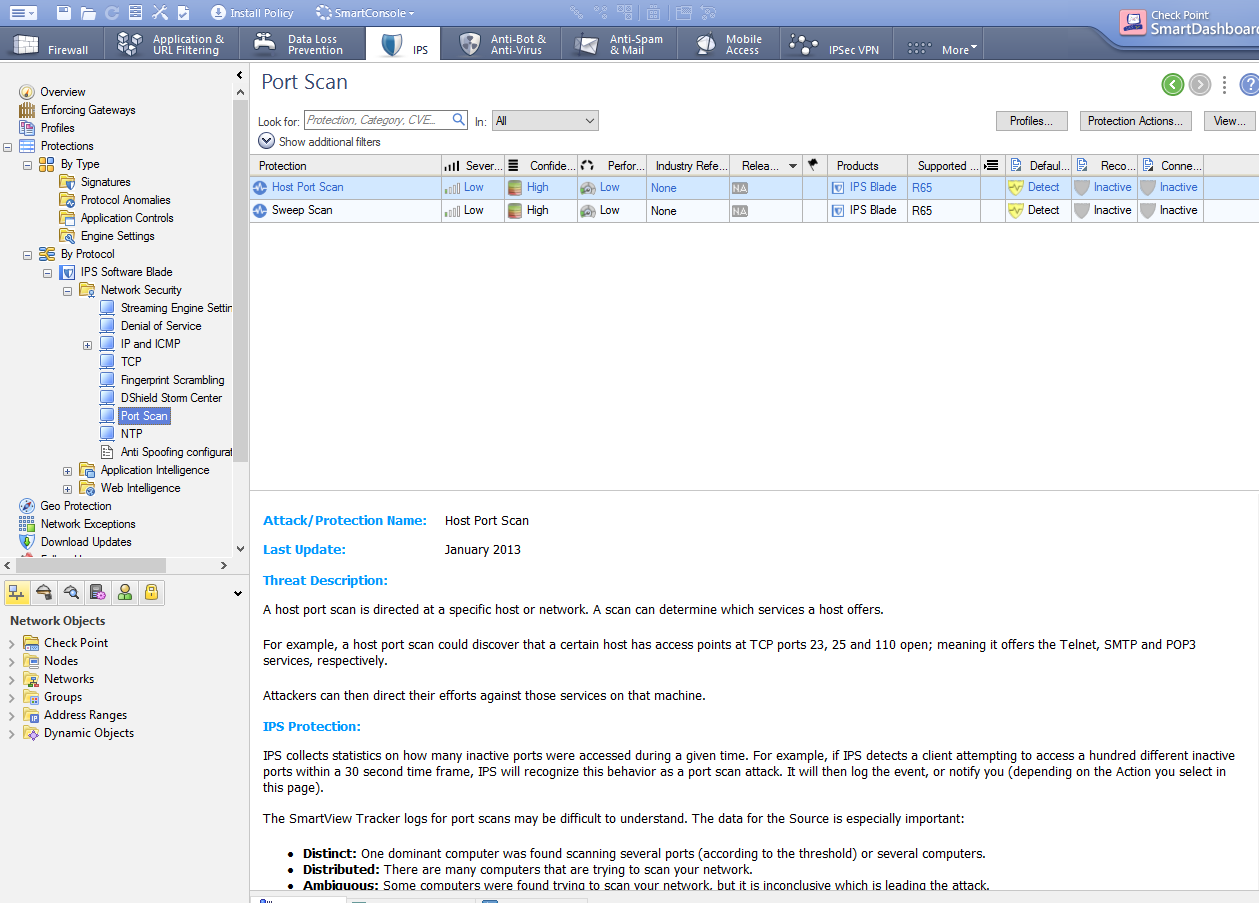
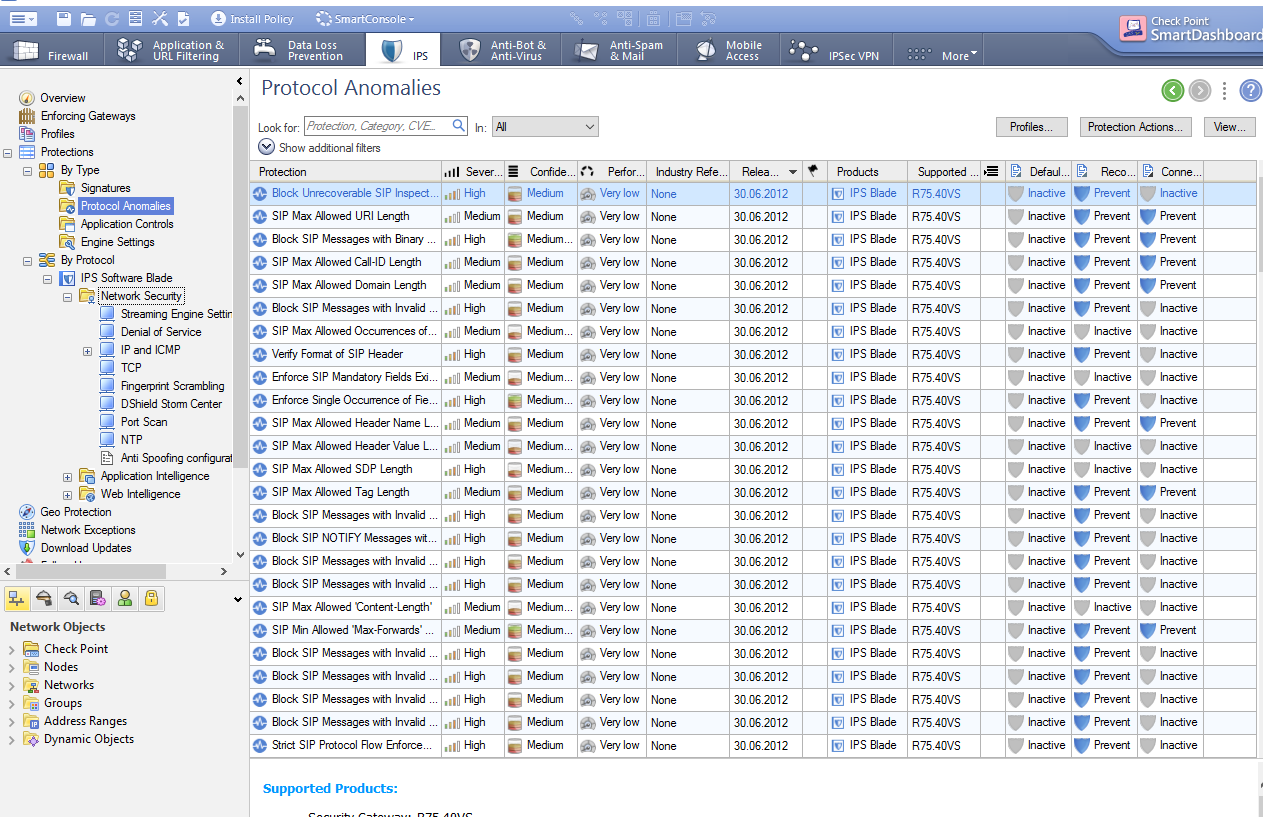
There is Intrusion Prevention System inside the firewall. This system detects potential cyber attacks, automatically blocks unwanted network activity, both incoming and outgoing, in automatic mode.
IP telephony
Prioritizing network traffic is another Check Point's task. In practice, this means no problems with ip telephony: there is no more ‘dotted line’ on the line. In addition to this, the firewall is responsible for secure network printing within the Customer's departments, direct access to voice services, corporate mail.
We are glad that we help our customers do their favorite business. And we do it using advanced technologies.
*The British short-haired cat Agatha and her hostess Svetlana Larina, IT Center web-director participated in the preparation of the publication. Sveta, go to the accounting department for a fee for the model!